For many IT leaders, achieving zero trust networking has evolved from an aspirational model to a necessary practice, especially with current hybrid work models, distributed IT and the security risks that come along with it. In recent years, the disparity of security built into IoT devices has raised alarms. Our increasing reliance on connected devices puts the spotlight on security measures that are inherently built into devices at manufacturing – or lacking through the manufacturing process.
Device manufacturers are responsible for ensuring device trustworthiness. Security-at-design is driven by zero trust manufacturing, an extension to the zero-trust networking model and an approach to building trustworthy electronic, industrial control and IoT devices within a supply chain that cannot be trusted. The model combines multiple technologies, applying them across the design, manufacturing, testing and product delivery phases to ensure trust at the owner or operator level. It can be applied to the simplest of devices, like electronic components, through to more complex equipment like smart meters, building automation controllers, medical devices and automotive control systems.
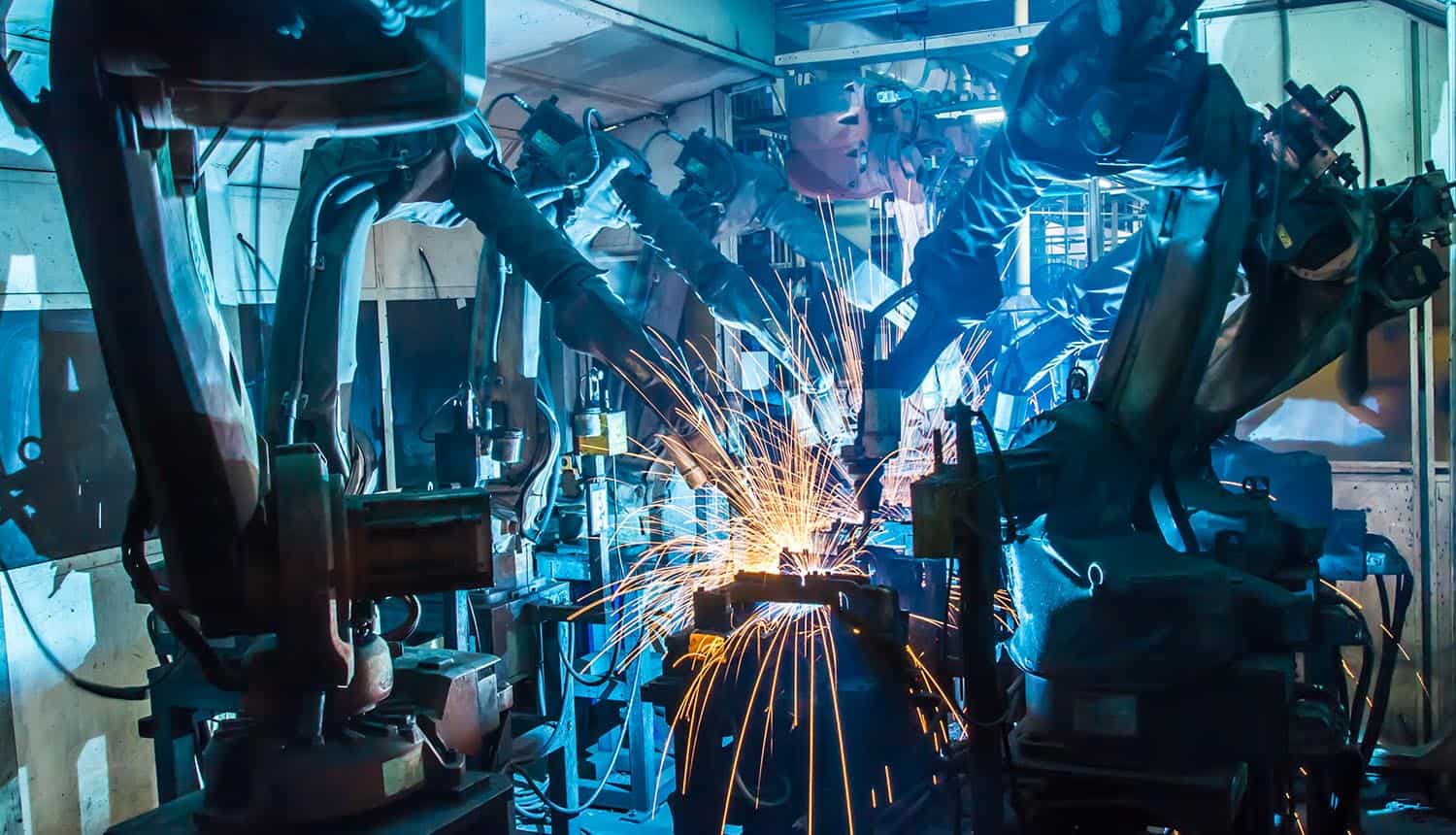
Traditional supply chains involve hundreds or even thousands of suppliers and companies who perform tasks to bring products to market. Take electronics manufacturers as one example, whose supply chain can include design partners, original equipment manufacturers (OEMs), contract manufacturers, component suppliers, contract software, logistics companies and systems integrators. Any one of those supply chain partners interact with partners of their own, contracting services to global vendors to minimize costs.
Complex supply chains make it difficult for manufacturers to produce devices that can be trusted by both the manufacturer and the device owner or user. Consider that billions of devices manufactured across this supply chain model are used in critical infrastructure like utilities, automotive, retail, healthcare and building automation.
In terms of security risks, the supply chain ecosystem is attractive to nation-state attackers and threat actors targeting IP theft. Stolen credentials including private keys and digital certificates are a rising threat and directly affect businesses. A recent study found that 73 percent of surveyed organizations experienced downtime due to mismanaged digital certificates. Ensuring that private keys and digital certificates are protected, kept private and managed securely is critical to protecting devices and applications against sophisticated cyber-attacks across the supply chain.
Generally speaking, OEMs are focused on meeting customer specifications. They hold responsibility for bringing products to market as fast and as cost effective as possible, and consequently security is often an afterthought rather than a key requirement designed at the start of the product lifecycle.
The reality is that devices are vulnerable to exploit throughout the supply chain starting at design, through to manufacturing, testing and delivery. Adopting a zero-trust approach is critical to managing supply chain risk and building assurance that the device hardware, firmware and credentials are secure and can be trusted.
Establishing a zero-trust manufacturing framework
A zero-trust manufacturing architecture considers several framework pillars including: hardware-based security, embedded security, public key infrastructure (PKI), key and certificate lifecycle management, device trustworthiness, code signing and authentication. Whether you’re starting from scratch or augmenting an existing framework, manufacturers can start by establishing these core best practices:
- Hardware-based security: Leverage device-based, tamper-resistant hardware secure elements, TPMs or hardware secure modules (HSMs) to create a trustworthy root of trust (RoT).
- Secure bootstrap certificate: Replace the initial bootstrap certificate with an updated certificate to ensure that the device boots up with the intended firmware.
- On-device key generation: Private keys should be generated and stored securely on the device so that it can attest to its own identity.
- Enable mutual machine-to-machine (M2M) authentication: Implement strong user access controls and M2M mutual authentication.
- Centralized code signing: Ensure that firmware updates are signed by the developer and authenticated by the device before being installed.
- Secure communication with end-to-end encryption: Implement encrypted SSL/TLS or IP VPN communications to ensure data privacy.
- PKI management: Implement and automate PKI and key/certificate lifecycle management.
When implemented holistically, a zero-trust manufacturing architecture will ensure that a product’s firmware, data and digital credentials can be trusted through every step of the manufacturing supply chain and beyond, while managing manufacturing supply chain complexity.
As a device manufacturer, accountability for robust security and a zero-trust approach has never been more important, especially as IoT related threats and vulnerabilities like Man-in-the-Middle attacks, unauthorized firmware updates, Root CA impersonation and IP threat and counterfeiting continue to increase.